Prime numbers and their importance to modern life
So, you’ve graduated high-school, or even made it through university. If you’re reading this article, we expect you to understand at least the basics of Prime Numbers. These numbers are incredible, and they are critical as the fundamental building blocks of all numbers. In addition, they help us understand the universe.
If aliens ever send us a message, it will be through prime numbers since no matter what century, lifestyle, or trend, Prime Numbers never change.
You are already probably familiar with what they are but if not, read ahead. Primes are the set of all numbers that can only be equally divided by one and themselves, with no other even division possible.
Numbers like 2, 3, 5, 7, and 11 are prime numbers, but few realize their importance and how mathematical logic imbues them into vital applications in the modern world.
Let’s see something cool about prime numbers. Mathematicians have shown that:
Absolutely Any Whole Number can be Expressed as a Product of Primes, Only Primes, And Nothing Else.
For example:
To get 222, try 2 * 3 * 37
36,230,980? Why, that’s just, 2 * 2 * 5 * 23 * 79 * 997
Or look at the tree of how the above primes are made up:
| 36230980 | ||||||
| / \ | ||||||
| 2 | 18115490 | |||||
| / \ | ||||||
| 2 | 9057745 | |||||
| / \ | ||||||
| 5 | 1811549 | |||||
| / \ | ||||||
| 23 | 78763 | |||||
| / \ | ||||||
| 79 | 997 |
Sometimes, you might find the calculation instead of 2 * 2 * 5 * 23 * 79 * 997 look like this: 22 x 51 x 231 x 791 x 9971, which is just the exponential form of writing the same arithmetic process.
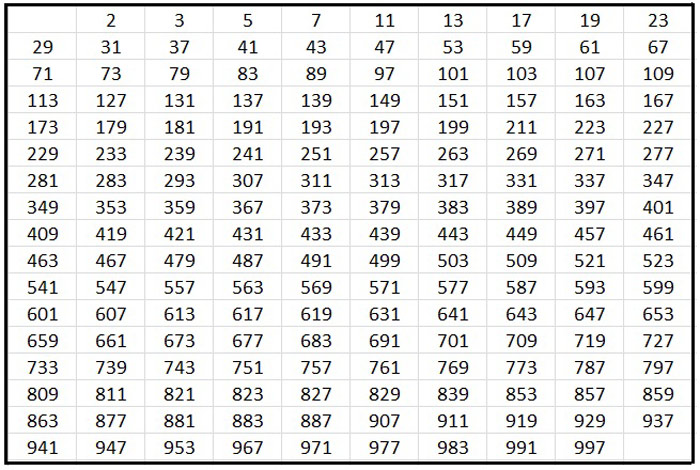
So now do some simple calculations on your own to get a feeling. For your convenience, we’ve attached a good list of Prime Numbers for you to try out. We have a table with all of them up to 1000.
This fundamental rule is called the “prime factorization rule” or in the more scientific terminology the “Fundamental Theorem of Arithmetic” [1].
You cannot pull apart a prime number any further. So as we try to pull apart any number into two numbers, then pull those apart into two numbers if possible, and so on, we will eventually be left only with Prime Numbers.
Some might argue that this is nothing more than a mathematical oddity. But there is another fact that adds importance: Mathematicians and computer scientists have determined that:
It Is Impossible to Establish an Efficient Formula for Factoring Large Numbers into Primes.
There are ways of factoring large numbers into primes. Still, if we try to do it with a 500-digit number—applying the same algorithm we will use to factor a 7-digit number—the world’s most advanced supercomputers [2] would take an absurd amount of time to finish calculating the building blocks of the number – or the Primes. To give you an idea of the scale: factoring a 500 digit number into its primes could take as long as the planet’s formation, and for huge numbers, the factoring process could take longer than the age of the universe itself.
As we can establish, the practical limit to the size of the numbers we can factor into primes is limited. This fact, however, is vital to modern computer security. So now, looking at the above problem from the perspective of computer security, we understand that there is a great interest to solve the problem, and being able to factor a large number into primes in a reasonable time is a need.
Most current encryption algorithms exploit the fact that we can easily take two large primes and multiply them together to get a new, super-large number. However, presently, no available computer can take that super-large number and quickly reverse into the two primes that comprise it.
This simple mathematical security is the base for the so-called public-key cryptography [3], or in other words, an encryption technique in which we do not require to worry about the essential public part of the key. This Public Key can be openly distributed (and is required to be distributed) to any third party that wishes to decrypt whatever content is encrypted with the key in question.
Knowing the public key to encrypted information won’t help you decrypt it. Before you can read the file or message, you must know the critical factors of the encryption key. And just as we explained above, this is not something you can figure out on your own.
Prime Numbers and Cyber Security
So how do you securely communicate the initial specifics needed to set up secure communication?
In public-key cryptography, which is the backbone of computer encryption, we can get around this because the specifics of getting into secure contact do not need to be protected themselves.
Precisely the opposite is the case - people post links to their public keys on social media, so as many people as possible will be able to encrypt messages for them. Though there are now quite a few encryption algorithms that exploit prime factorization, the most historically significant and still conceptual blueprint for the field is RSA [4].
There are two types of commonly used encryption systems: symmetric encryption and asymmetric encryption.
Symmetric encryption is high-speed but also not all that safe. It uses the same key for encryption and decryption, and if that anyone untrustworthy finds that key, they can compromise your entire encrypted data. This type of encryption usually participates in computer or mobile transactions.
You might have noticed that you get sent a security code while online banking- this code is a symmetric encryption code.
Besides being unsafe, the key needs to circle all members before use. Here is where the magic of asymmetric encryption comes in.
Asymmetric encryption uses two keys instead of one. One is for encryption, and the other – for decryption. This approach works because one key is public (encryption), and the other is private (decryption). Therefore, only those with a private key can understand cipher after decryption, protecting the information from any online hacker or an untrustworthy user.
This encryption method works and provides a lot of security because of its trapdoor features. Everyone with a public key can encrypt but going back to decryption is not possible.
The image makes it easier to understand the function of the trapdoor. RSA, the most used encryption, also uses an asymmetric encryption method.
RSA is an encryption system whose development includes the knowledge of simple facts about numbers. This system secures information online, and it is a preferred method because the numbers broken down into prime numbers are multiplied.
For example, if 11 and 17 are multiplied to get the number 187 when broken down, it will give the same two numbers. Therefore, the larger the number, the stronger the encryption will be.
We use computer encryption all the time, e.g., when communicating our credit card information to an online merchant, logging into our bank, or sending a manually encrypted email to a colleague. In summary, this means we rely on prime numbers throughout our virtual life – day in, day out.
To understand prime numbers is no senseless quest nor a purely scientific challenge. It is, instead, the greater understanding of the limitations of all our security, especially if one considers that there has been no progress in factoring large numbers for several years now.
Researchers have networked several hundred computers together and spent the equivalent of what it would take a single computer around several thousands of years to complete. It uses advanced factoring algorithms to factor the “RSA-768″ number — that is to say, a number with 232 digits put up by the RSA group as a factoring challenge.
Proving it was possible to break 768-bit encryption in non-universal-heat-death timescales is unacceptable for the world of security experts. As a reaction, the standard for modern encryption moved on to RSA-1024, using numbers with 309 digits and RSA-2048 with 617 decimal digits.
Prime Numbers in Quantum Computing
1024- and 2048 bit encryptions are supposed to be safe from anyone not in possession of a time machine, as far as we know — however lately novels like Digital Fortress by Dan Brown [5] and Contact by Carl Segan [6] refer to a secret NSA project, which supposing is in the possession of secret Quantum Computer Technology [7] which can chew through even 2048-bit encryption in a reasonable time.
Quantum Computing is lately heavily in the press, and Google and NASA work on a project to make it a new standard. However, there is no evidence that it can break numbers based on 1024- or 2048-bit encryption.
The Quantum Computing Algorithm was discovered in 1994 by Peter Shor. His algorithm was great for integer factorization, which is that you put in an integer number, and it calculates its prime numbers.
This algorithm has been quite successful in decryption, and it can also factorize smaller prime numbers. However, it has not yet been able to decrypt the RSA scheme. The research is still ongoing, and the day it becomes successful, all concepts of online privacy will crumble down.
The decryption of prime numbers is a million-dollar question. No, really. The Clay Mathematics Institute in Cambridge has put up a million-dollar prize for anyone who can show proof of the Riemann Hypothesis.
You might question how the Riemann Hypothesis is related to Quantum Computing. Well, the connection between the two means a new method of quantum computing that can potentially decrypt prime numbers.
Using the Riemann Hypothesis would propose that prime numbers are divided predictably, like the zeros in the Riemann-zeta function. Proving this will also solve the million-dollar question.
Many mathematicians believe that the only accurate method of decryption is going to take place through quantum computing. As of now, the focus is on experimental implementations of quantum computing.
There is particular importance to prime number factorization as the fundamental building block of all numbers, which are the root for understanding the universe [8].
Some mathematicians describe number theory a little bit like archaeology. The feeling isn’t one of inventing modern technologies but of uncovering the logical foundations of the universe, those that describe its behavior everywhere, throughout all of the time.
The CodeCoda Research Lab, inspired by Digital Fortress, works on a concept for a new Encryption Algorithm that makes it impossible to break by factoring numbers. Therefore the “Fundamental Theorem of Arithmetic” is one of the building blocks of such an algorithm. A detailed understanding of Prime Numbers is vital to building the next generation of quantum-safe encryption.
Despite such an uproar, the possibility of decryption would not mean the end of security. Even though quantum computing will be able to decrypt cipher, there is already plenty of security technologies that have been developed and set in place beforehand.
Importance Of Prime Numbers in Modern Life
We can integrate Prime Numbers into our lives at different levels. For example, even for communicating our credit card information to online stores, we use prime numbers.
One of the essential things to understand about prime numbers is that they have exceptional properties in factorization. One of them is that it is elementary to find larger prime numbers. However, they are harder to factorize.
Prime numbers are essential for communications, and most computer cryptography works through them. Not only this, but file encryptions also work through prime numbers. Whether it is communicating your billing information, logging into an account, or even emailing, it is all using encryption.
The encryption or security that hides our personal information from being readily available is also the work or prime numbers. This feature shows that prime numbers are essential in the modern, technology-related way of life. Therefore, any limitation in the field of prime numbers is a limitation that we all face and will feel.
The decryption happens through the factorization of more significant prime numbers. However, this factorization is only for temporary use. Actual factorization of prime numbers is impossible even for a supercomputer. Nevertheless, there is hope that quantum computers in the future will be able to solve this problem.
Prime numbers are also sitting comfortably on our computer screens – they intensify the color of pixels. They are also used to get rid of harmonics in products by manufacturers. Moreover, they make up the basic computer security, which is vital in the age of easy exchange of information.
Many theorists give much importance to prime numbers because they are the foundation of whole numbers. However, they are also numbers with odd mathematical properties and find wide applications in the current technological era.
The role of prime numbers is also visible outside our carefully constructed world – in nature. For example, scientific research shows that cicadas insects use prime numbers to lay their eggs and exit their burrows. They leave in intervals of 7, 13, or 17. Thus, scientists propose that they adopt prime numbers to prevent predators from evolving and preying on them. In other words, these insects rely on prime numbers to survive.
Prime numbers are prevalent in popular cultures. Many singers, writers, and artists have taken inspiration from it. Carl Sagan, for example, wrote a book about communication with aliens through prime numbers. These positive depictions and understandings inspire people working outside the scientific or mathematical fields.
Even the top-rated game called Candy Crush uses scientific theories and mathematical principles, most of which would not have existed if it were not for prime numbers. For example, the number theory never would have seen the light of day without prime numbers.
Whatever your opinion may be about these unique numbers, there is no denying that they are a fundamental aspect of the universe. The ongoing research will help us in prime human development.
Prime numbers have immense potential with intensive application in many remarkable projects. In addition, we may learn about the world and numerous technical accomplishments by intensively studying them.
References

